Financial Literacy Month
April is Financial Literacy Month. Check out our podcasts, videos, articles, songs, lesson plans and activity guides, we’ve got something for everybody.
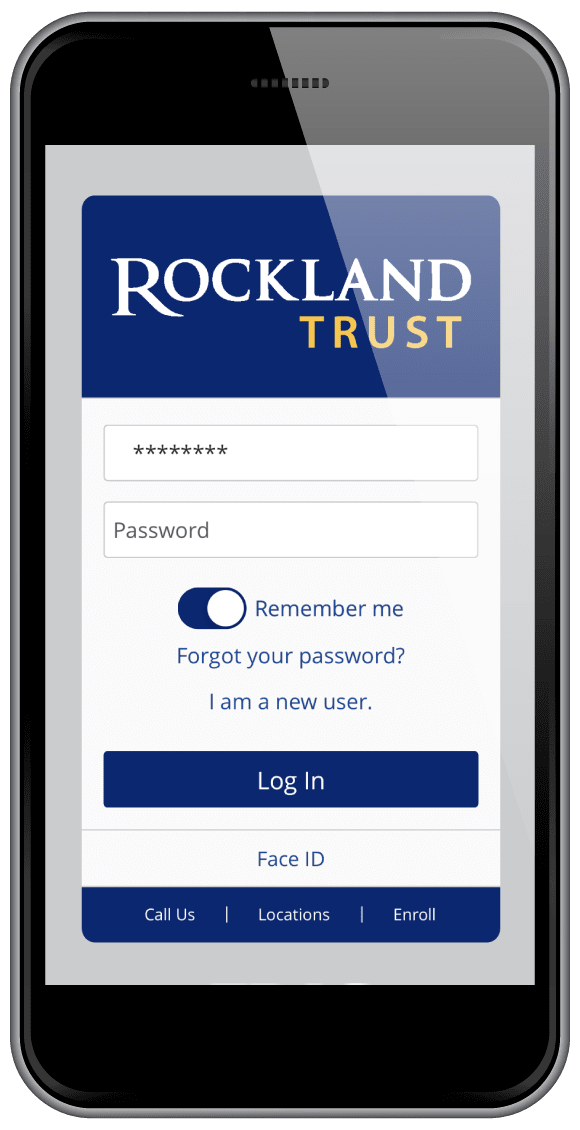
We know your time is valuable. That's why we make it as easy as possible to take care of your financial business online and with your mobile device.